The web is livelier than ever, driven not only by human visitors but also by a rapidly growing number of automated bots, crawlers, and AI-powered tools scanning websites for content and data around the clock.
While some bots are beneficial—like search engine crawlers that help surface your site—others can distort your analytics data, artificially inflate your traffic numbers, and even lead to unnecessary usage of your hosting resources.
This guide explores how to leverage Cloudflare’s robust free security features—including Bot Fight Mode, JavaScript and managed challenges, and other key Cloudflare settings—so you can minimize unwanted bot traffic, safeguard your WordPress site, and ensure your server resources are dedicated to genuine visitors.
Table of Contents
Setting up Cloudflare for bot protection
You don’t need a paid Cloudflare subscription or intricate setup to shield your site from unwelcome bots. Cloudflare’s free plan already equips you with essential tools that can significantly reduce bad bot traffic.
Let’s look at how to get everything set up, step by step.
Connect your site to Cloudflare
If your WordPress site is hosted on a platform with built-in Cloudflare integration, you enjoy performance and CDN advantages right out of the box. To unlock the full range of Cloudflare security tools, however, it’s important to link your own Cloudflare account.
The connection process is streamlined and only takes a few minutes. Zero in on a thorough walkthrough that covers everything—from adding your domain to updating your DNS records and nameservers. Get your site connected by following this resource:
👉 How to install and configure Cloudflare on your WordPress site
Once your domain is active on Cloudflare, you’re ready to activate additional features that prevent unwanted bot and scraper traffic, all while keeping things smooth for your legitimate users.
Enable bot fight mode
After your site is linked to Cloudflare, enabling Bot Fight Mode is a fast and effective way to begin filtering malicious automated traffic.
This no-cost Cloudflare feature works to spot and deflect bots attempting to crawl, scrape, or overload your site—even those designed to mimic human behavior.
To enable Bot Fight Mode, follow these steps:
- Go to Security > Settings from the left-hand menu.
- In the Filter by section, select Bot traffic.
- Look for Bot Fight Mode and toggle it on.
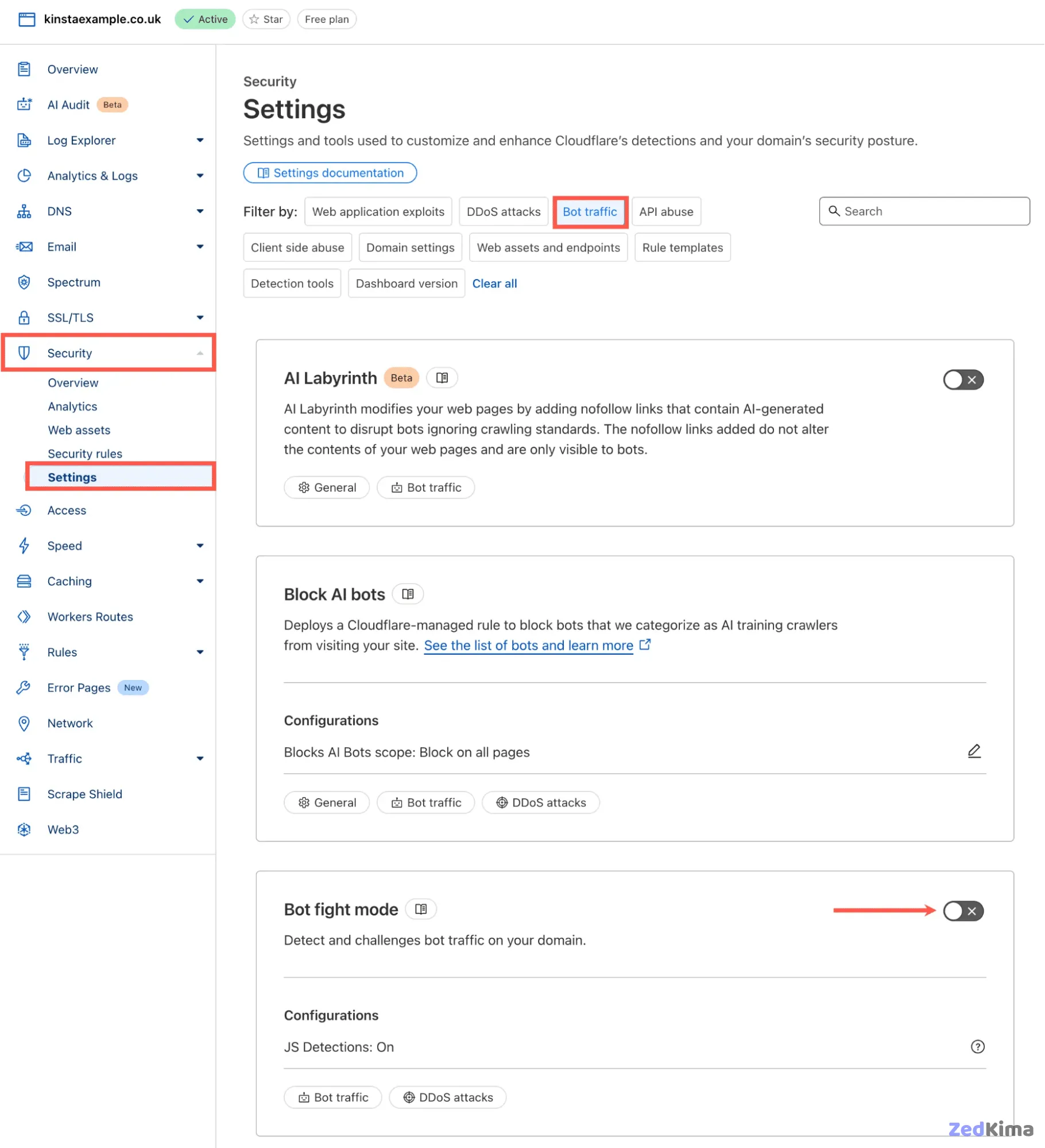
Once active, you can track the impact in your analytics dashboard, where you’ll likely spot a decrease in visits as Cloudflare blocks more non-human attempts before they ever touch your site.
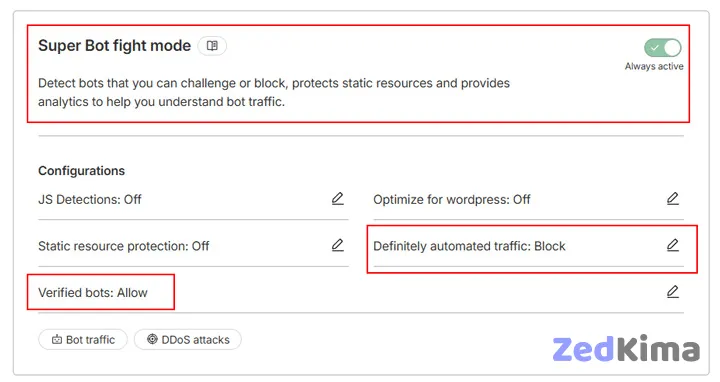
If you’re subscribed to a paid Cloudflare plan, you can also access Super Bot Fight Mode, which offers advanced protection. This version lets you customize responses for various bot types, using JavaScript detection to catch sophisticated headless browsers and stealthy scrapers.
For instance, instead of blanket blocking all bot activity, you might choose to only block “definitely automated traffic” and freely permit “verified bots” such as those from known search engines:
Set up JavaScript and managed challenges
Even with Bot Fight Mode activated, some advanced crawlers or automated tools may still get through by imitating legitimate browsing.
Cloudflare’s security rules give you the flexibility to apply challenges—extra steps required to verify visitors are human—before letting them in.
Rather than applying these challenges site-wide, it’s best to target high-risk areas of your WordPress site, such as:
/wp-login.php(WordPress login screen)/xmlrpc.php(a frequent bot target)/wp-admin/(your admin dashboard)
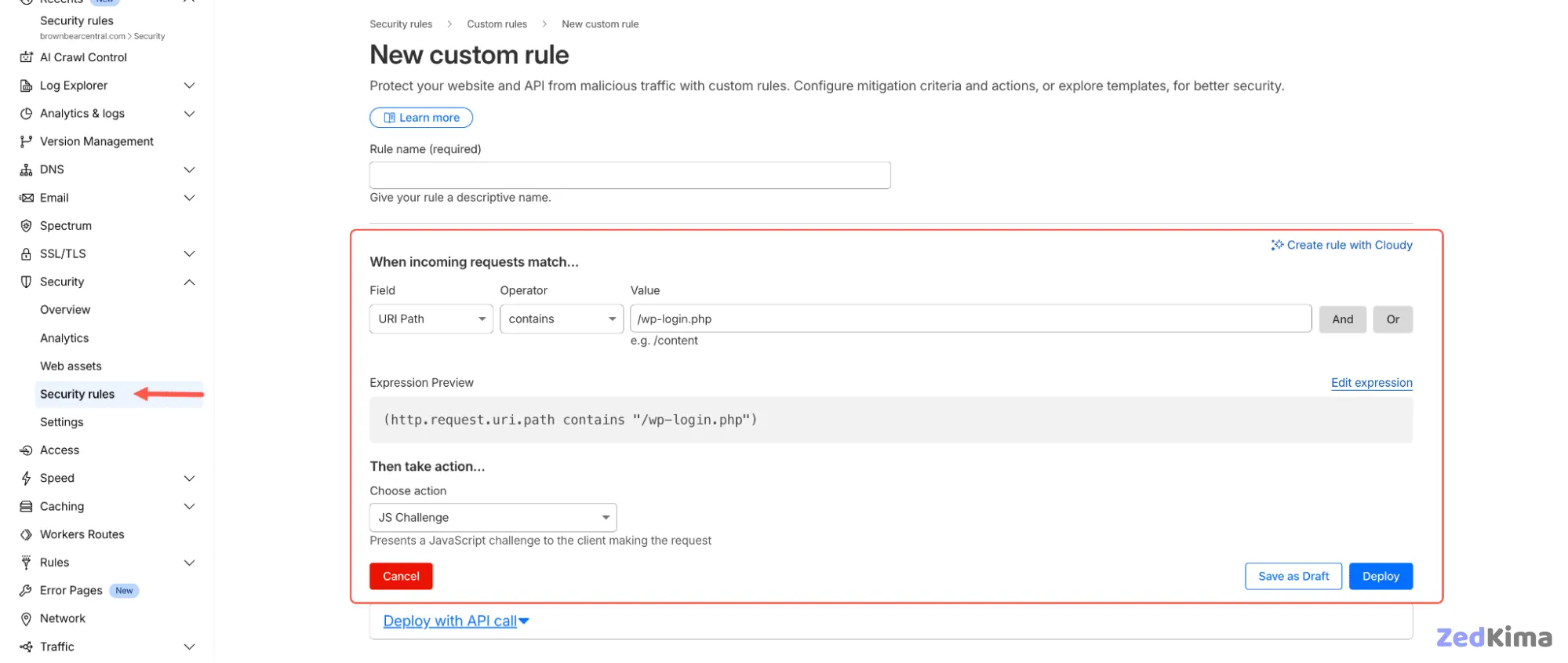
To set up a JavaScript or Managed Challenge rule:
- Navigate to Security > Security Rules.
- Select Create rule > Custom rules.
- Assign a Rule name (like JS Challenge for wp-login).
- For When incoming requests match, configure:
- Field: URI Path
- Operator: contains
- Value:
/wp-login.php
You can enhance the rule further by selecting Edit expression to add more conditions, like the example below:
(http.host in {"example.com" "www.example.com"} and
starts_with(http.request.uri.path, "/wp-admin") and
not cf.client.bot and
not http.request.uri.path contains "/wp-admin/admin-ajax.php")The sample above focuses on the /wp-admin path, bypasses verified bots, and skips the AJAX endpoint needed for WordPress functionality.
For the action, select one of these options:
- JavaScript Challenge – prompts each visitor with a brief browser verification.
- Managed Challenge – lets Cloudflare decide when to prompt visitors, based on AI evaluation of risk and visitor behavior.
Hit Deploy to activate your rule. If you’d like to test it out before going live, choose Save as Draft.
Monitor the results
After enabling Bot Fight Mode or applying your Cloudflare rules, it’s important to monitor if the changes are successfully filtering unwanted traffic and helping keep your analytics accurate.
Utilize both Cloudflare’s and your hosting dashboard’s analytics tools to measure how effective these settings are. Here’s how to review your traffic data using both platforms.
Check Cloudflare’s security analytics
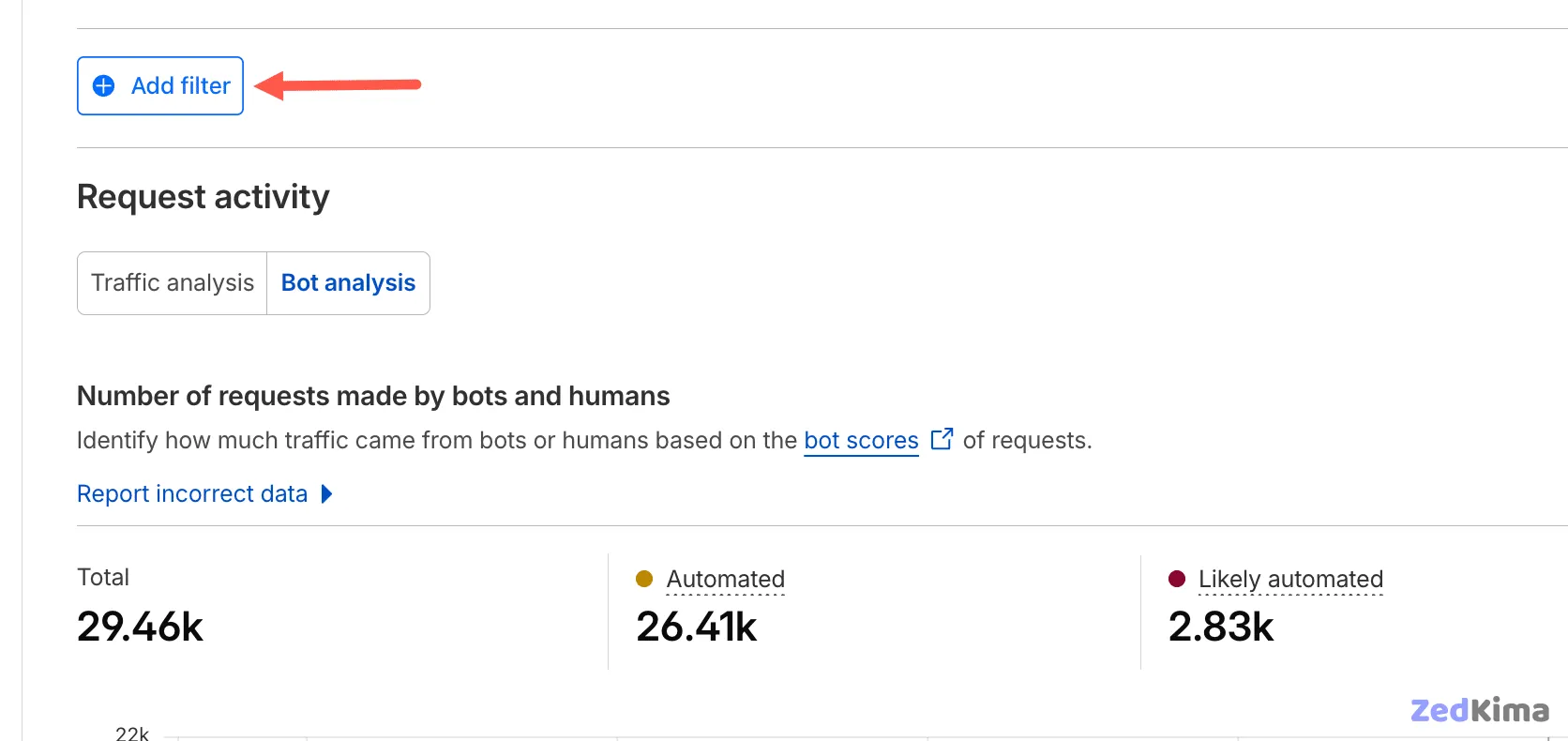
Within the Cloudflare dashboard, head to Security > Analytics > Bot Analysis.
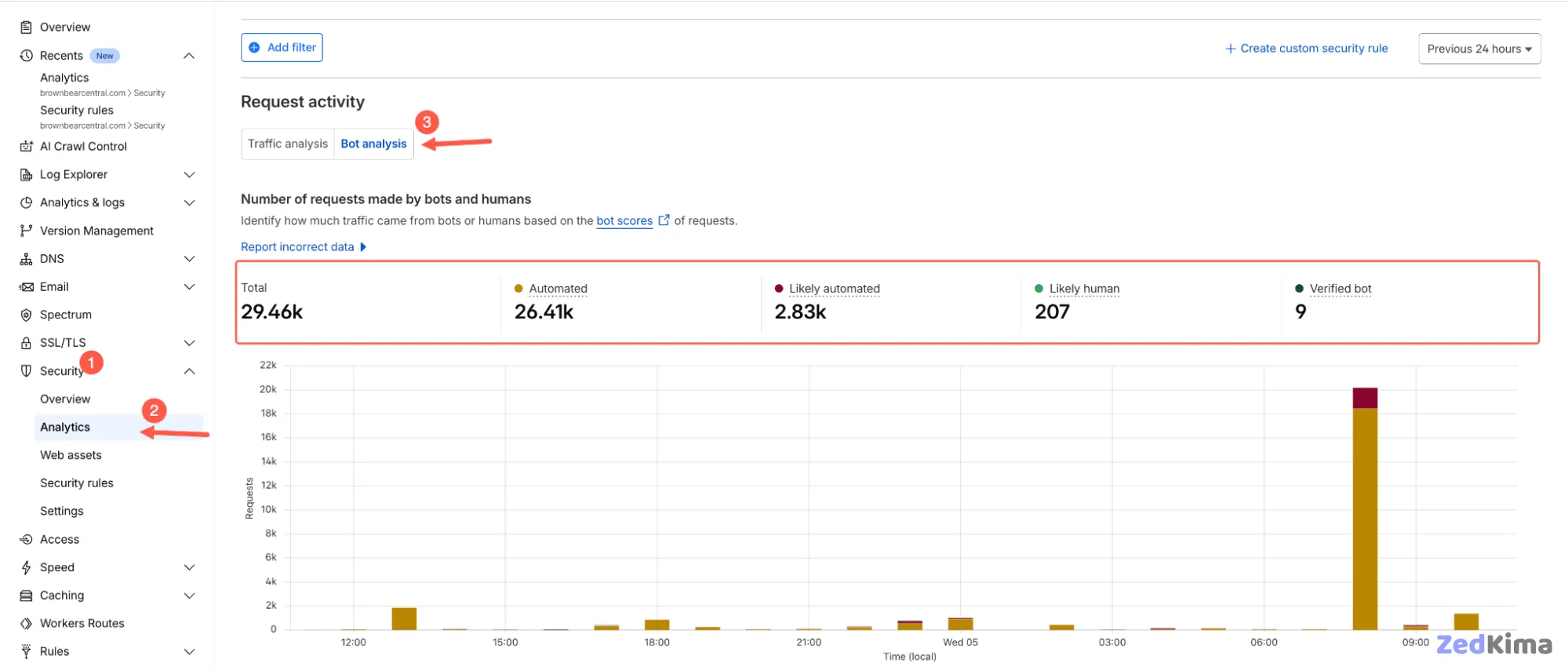
This section gives you a straightforward breakdown of site traffic by source—human visitors versus bots.
Cloudflare assigns each request a bot score, drawing on behavioral cues and machine learning. Traffic is classified according to types such as:
- Automated – Clearly detected as non-human bots.
- Likely automated – Suspicious, bot-like behavior (like headless browsers or scrapers).
- Likely human – Standard browsing activity from real users.
- Verified bot – Validated bots like major search engines or payment processors.
The Bot Analysis chart updates in real time. Use its filters—by country, IP, device, and browser—to pinpoint frequent sources of unwanted automated hits.
Understanding the Types of Bots and Their Impact
To make informed decisions about bot management, it’s important to distinguish between the types of bots that visit your site and the unique risks they pose:
- Good Bots: Examples include Googlebot, Bingbot (search engine crawlers), and other verified bots that support accessibility or monitoring. These generally improve your site’s visibility and are usually welcome traffic.
- Bad Bots:
- Scrapers – Steal your content for use elsewhere, possibly hurting your SEO.
- Credential Stuffers – Attempt login with stolen or common passwords, posing a security threat.
- Spam Bots – Fill comment forms or registration pages with spam links.
- DDoS Bots – Overwhelm your site with requests, potentially causing outages.
Identifying which bots to allow and which to block is key for efficient bot management and resource conservation.
Best Practices for Fine-Tuning Cloudflare’s Protection
Beyond enabling Bot Fight Mode and configuring basic rules, several additional strategies enhance Cloudflare’s effectiveness:
- Whitelist trusted bots: Use Cloudflare’s “verified bots” exemption to ensure essential crawlers (like search engines) aren’t accidentally blocked. Maintain an updated allowlist if your site needs to interact with third-party APIs or services.
- Implement rate limiting: Set rate-limiting rules on login and registration endpoints to prevent brute-force attacks and slow down high-frequency scraping attempts. Cloudflare can block or challenge IPs sending requests above a certain threshold in a specified time period.
- Leverage Cloudflare’s Threat Intelligence: Explore the Threat Intelligence feed to proactively identify IPs associated with malicious activity and preemptively block or challenge them with custom firewall rules.
- Optimize CAPTCHA and challenge frequency: Avoid over-challenging human users by configuring custom rules and exceptions—for example, skipping the challenge for logged-in users or whitelisted IPs, while applying stricter checks for sensitive endpoints.
Examples of Practical Cloudflare Rules
- Country-based blocking: If your audience is localized, consider applying a Managed Challenge or outright block to countries where legitimate traffic is unlikely, reducing unnecessary bot visits from high-risk regions.
- Filter IP addresses by behavior: If your analytics reveal repeat offenders (IP addresses persistently hitting sensitive endpoints), block or challenge these directly with Cloudflare’s IP Access Rules.
- Dynamic content protection: For membership, ecommerce, or forum sites, restrict access to user-specific or commercially sensitive information using layered security: combine cookie-based or session-awareness in Cloudflare rules for maximum protection.
Integrating with WordPress Security Plugins
While Cloudflare handles traffic at the edge, supplementing with a WordPress security plugin adds another layer of protection inside your site:
- Plugins like Wordfence or Sucuri can detect suspicious behavior that escapes Cloudflare, such as unexpected admin access or malicious file uploads.
- Login security enhancements: Add reCAPTCHA, two-factor authentication, or limit login attempts for tighter user access controls—these measures reduce the remaining risk from sophisticated manual attacks.
Coordinating Cloudflare’s bot filtering with in-site security methods creates multiple hurdles for attackers and further preserves legitimate user experience.
Advanced Analytics and Ongoing Maintenance
Bot management is not a one-time setup—it requires periodic review and adjustment as both legitimate and malicious automated traffic evolves:
- Monitor trends: Look for changes in traffic patterns over weeks or months, as spikes or drops in bot traffic may signal new threats or the need to revise allow/deny lists.
- Respond to false positives: If you notice real users or beneficial bots being blocked, review and adjust your rules to reduce friction without weakening security.
- Regular rule audits: Quarterly audits of your Cloudflare rules and analytics ensure your filters remain relevant, concise, and effective against the latest bot behaviors.
- Automate notifications: Use Cloudflare’s alerting features or integrate with external monitoring tools to receive instant notifications of security rule triggers or significant traffic anomalies.
Summary
Controlling unwanted bot traffic is an ongoing necessity for anyone managing a modern website. Using Cloudflare’s free tools, you can effectively block automated crawlers and scrapers before they cause problems for your site or hosting.
For WordPress site owners, especially those using cloud hosting, combining Cloudflare’s protections with your existing setup gives you high-quality insights and keeps website resources focused on authentic users. Consider hosting and bandwidth plans that match your needs for even more predictable costs and resource management.
By pairing Cloudflare’s advanced filtering with your site analytics, you can invest your energy where it matters: your content and your community—not fending off bots.